Par Baka DIOP – TheExpert SQUAD : AppSec Techleader ; Experte SecApp, DevSecOps / Decurity by Design
Définition
Le terme "applicative" renvoie directement à la couche 7 Application OSI. La norme ISO 27034 donne une définition complète de la sécurité applicative démontrant que la sécurité applicative ne couvre pas uniquement la partie logicielle mais aussi tous les contrôles et mesures de sécurité dans le cycle SDLC de l’application.
Chiffres clés
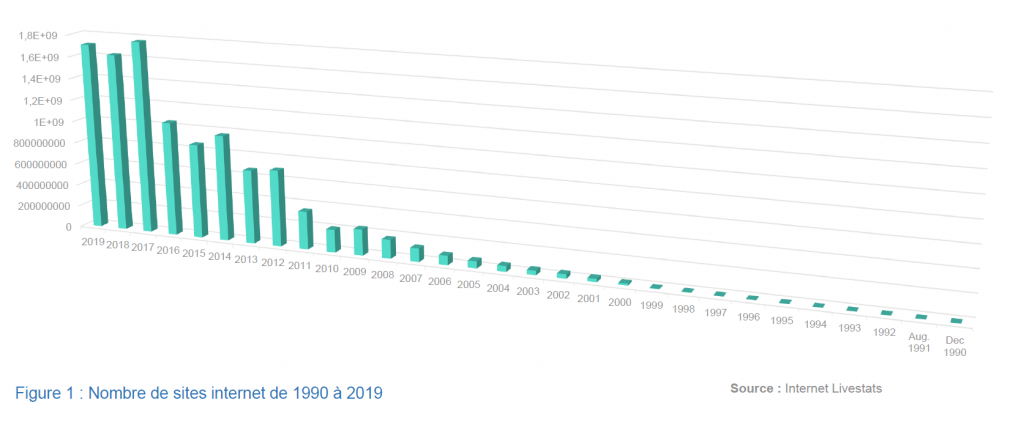
Le premier site Internet est apparu en décembre 1990. En 2019 plus de 1.5 milliard de sites internet ont été recensés (Figure 1).
Le nombre de sites web ne prend pas compte des applications mobile,s qui dépassent les 2 millions d’applications. On peut apercevoir dans la figure 2, le nombre d’applications Android disponibles sur Google Play.
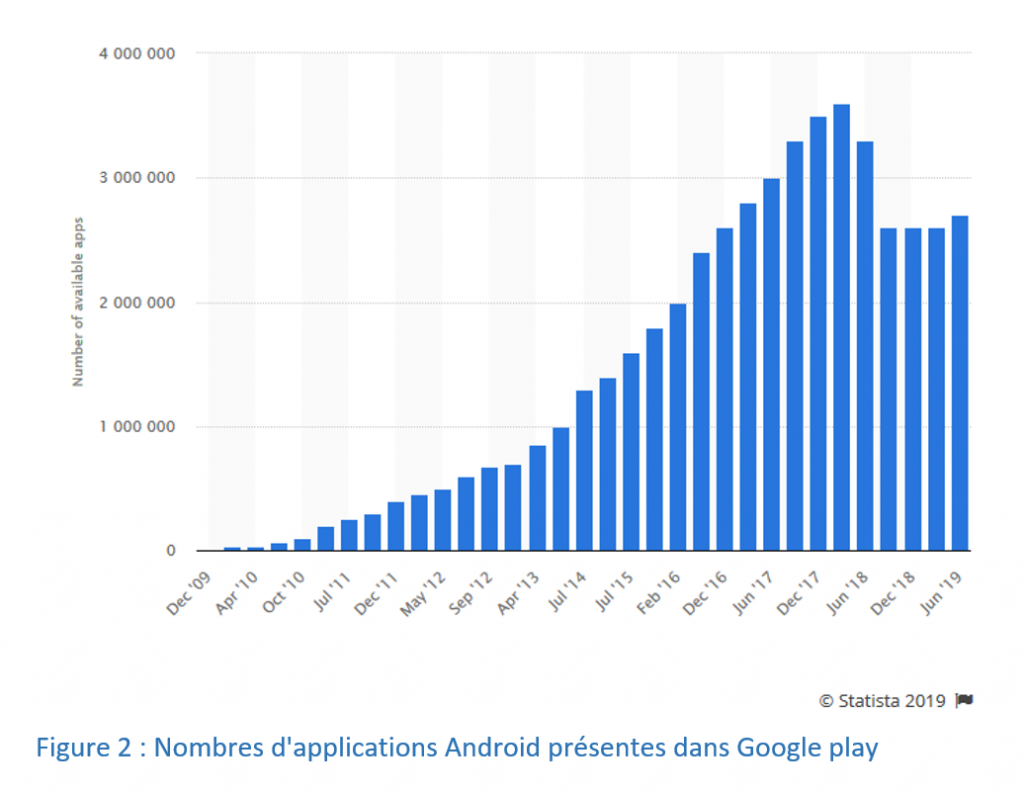
Ces chiffres montrent la rapidité et la croissance des apparitions des applications. Mais, la métrique dont on ne dispose pas, c’est la maturité des contrôles effectués sur ces applications.
Quelques questions sont à prendre en compte pour le suivi, à savoir la gestion de la sécurité de ces applications :
- Est-ce que des revues de codes sont faites avant de mettre en production ?
- Comment le risque est-il géré pour certaines applications ?
Sur ces questions fondamentales repose l’importance de la sécurité applicative au sein des entreprises.
La figure 3 montre le pourcentage des attaques effectuées sur une période d’une année mondialement, par pays.
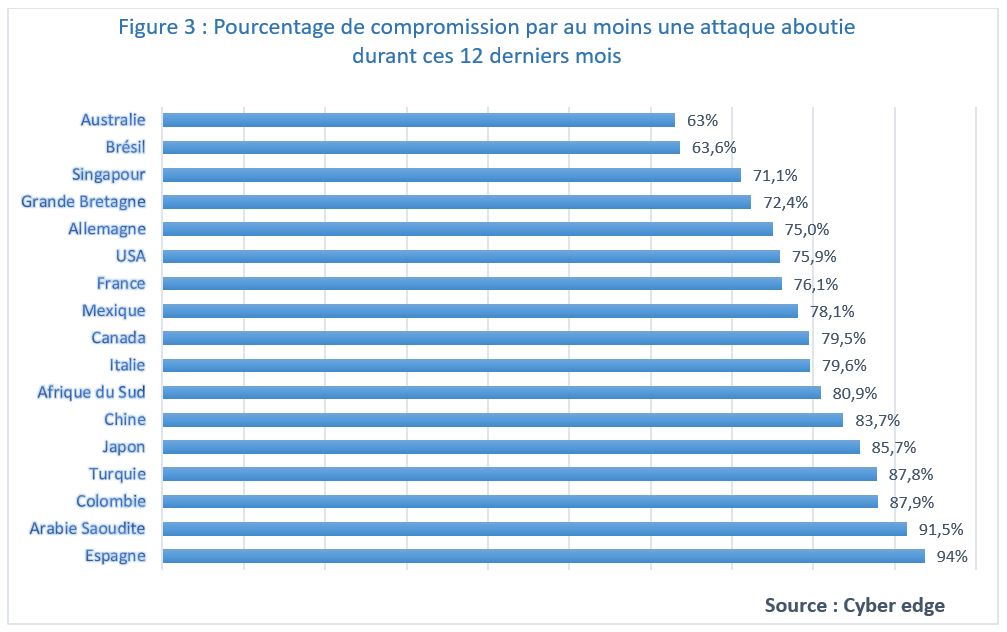
Ces chiffres appellent à une prise de conscience et des mesures de sensibilisations s'imposent dans la sécurité à mettre en œuvre.
Certaines failles récurrentes et récidivistes sont listées dans la figure 4.
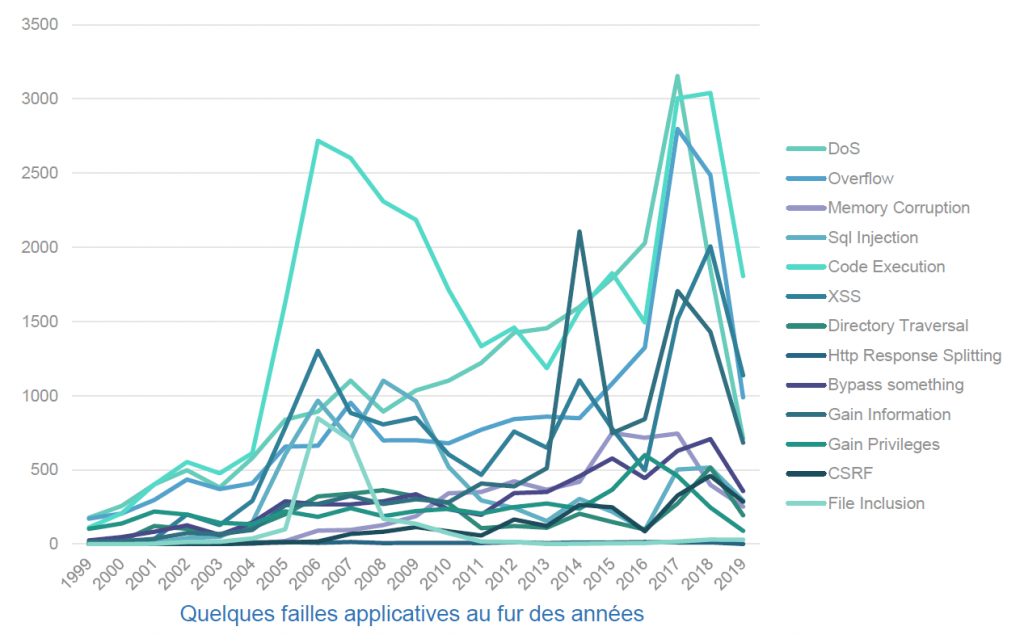
L’analyse de ces chiffres réaffirme le risque représenté par le niveau de sécurité des applications pour une entreprise quels que soient :
- La taille de l’organisation,
- Le lieu,
- La stratégie de sécurité (Security by design).
La connaissance de la sécurité applicative passe par la connaissance de ses fondamentaux.
Top10 OWASP
Open Web Application Security Project (OWASP) est une entité regroupant des experts travaillant sur la sécurité applicative, afin de mettre à disposition des produits open source (documents, outils, etc).
Parmi leurs publications, se trouve une liste des 10 failles les plus présentes dans les applications. Cette liste permet de sensibiliser sur les failles inhérentes ou nouvelles affectant les applications. La première liste date de 2007. Elle a été mise à jour en 2010, 2013 et enfin en 2017.
Voici la liste 2017 OWASP :
- A1: Injection
- A2 : Contournement des mécanismes de gestion d’authentification et de session
- A3 : Exposition de données sensibles
- A4 : Entités XML externes (XXE)
- A5 : Contournement des contrôles d’accès
- A6 : Mauvaise configuration de sécurité
- A7 : Cross-Site Scripting (XSS)
- A8 : Désérialisation non sécuritaire
- A9 : Utilisation de composants avec des vulnérabilités connues
- A10 : Journalisation et surveillance insuffisantes
Cette liste top 10 OWASP sera détaillée et analysée à l'occasion d'un article dédié.
Conclusion
Nous sommes actuellement dans une ère où il n’est plus possible d’ignorer l’impact qu’à la sécurité des applications dans une entreprise. Avec tout le niveau de sécurité du monde, il est d’abord important de ne pas oublier l’aspect humain dans l’histoire. Il faut une bonne sensibilisation et une bonne politique entreprise qui définisse avec clarté les règles mises en place. La sécurité applicative ne traite pas uniquement le code source, elle concerne également l’ensemble des composants allant des processus, les intervenants, les serveurs (machines), l’hébergement, au code source de l’application.
Sources
https://www.internetlivestats.com/total-number-of-websites/
https://www.symantec.com/fr/fr/security-center/threat-report
https://royal.pingdom.com/how-we-got-from-1-to-162-million-websites-on-the-internet/
https://cyber-edge.com/wp-content/uploads/2019/03/CyberEdge-2019-CDR-Report.pdf
https://www.cvedetails.com/vulnerabilities-by-types.php
https://www.owasp.org/index.php/Category:OWASP_Top_Ten_Project
https://www.owasp.org/images/7/72/OWASP_Top_10-2017_%28en%29.pdf.pdf
https://www.scassi.com/sites/default/files/SCASSI-27034-SECU-APPLICATIVE-201407.pdf
https://www.owasp.org/images/6/64/ISO_27034_review_(OWASP_Toronto_May_10,_2012).pdfhttps://www.iso.org/obp/ui/fr/#iso:std:iso-iec:27034:-1:ed-1:v1:en


