
S’il y a un rendez-vous incontournable mondialement pour le monde de la cybersécurité, c’est bien la #DEFCON27.
Franck CECILE était notre envoyé spécial sur place et il vous livre ses impressions personnelles sur la #DEFCON27.
Par Franck Cecile – TheExpert Cybersécurité Squad
> A lire aussi :
- Squad à la #DEFCON27 (2/3) : Mon expérience
- Squad à la #DEFCON27 (Part 3/3) : Mon ressenti
Disclaimer
Je tiens à préciser que cet article est rédigé avec mon point de vue personnel, et n’engage que moi, en gardant bien à l’esprit que :
- Les problématiques liées à la langue ont pu générer un gap dans la compréhension de certains aspects techniques,
- Suite à une annulation de vol, je n’ai pu passer que 2 jours sur place, et n’ai ainsi pas pu tout explorer (sachant que c’était ma première convention du genre),
- Mes compétences purement techniques dans le domaine du hacking sont assez limitées, comparée à des visiteurs très pointus en la matière.
Pour le reste, j’espère que l’article vous plaira, au moins autant que la DEF CON m’a plu !
Summary:
- La DEF CON, quèsaco ?
- C’est quoi ?
- Ça parle de quoi ?
- Comment ?
- C’est où et quand ?
- C’est pour qui ?
- Mon expérience à la DEF CON
- Qu’est-ce que j’y ai fait, qu’est-ce que j’y ai vu ?
- Dans le détail ?
- Mon ressenti personnel.
1. La DEF CON, quèsaco ?
C'est quoi ?
Pour ceux qui ne savent pas, on va reprendre Wikipédia : "La DEF CON est la convention hacker la plus connue à travers le monde. Elle est tenue chaque année à Las Vegas. La première convention DEF CON s'est déroulée en 1993." J’ai donc participé à la #DEFCON27, se déroulant juste après / pendant la BLACK HAT, autre grosse convention de hacker, également à Las Vegas. Avec plus de 20 000 participants ces dernières années, la DEF CON est une des plus grosses conventions de Sécurité Informatique au monde. Excusez du peu.
Ça parle de quoi ?

De Hacking. Bon, c’est un peu générique dit comme ça, mais justement. La force de la DEF CON, c’est de parler de hacking, en général ! Pour rappel, le hacking consiste à rechercher des moyens de contourner les mesures de sécurité, de protection, ou de défense en place, sur un système (ou un ensemble de systèmes) informatisé, numérique, voire même électronique ou physique.
La DEF CON met donc en avant la découverte de vulnérabilités et les possibilités d’exploitation d’équipements d’infrastructure réseau, d’ordinateurs, de smartphones, de systèmes de contrôles industriels (ICS/SCADA), d’appareils photo, de composants électroniques, d’objets connectés/IoT (aspirateurs, réfrigérateurs, lampes, serrures, thermostats, montres, sextoys… oui oui, vous avez bien lu, il y’avait une présentation sur des tests de pénétration – sans mauvais jeux de mots – sur un plug anal… les mecs savent s’amuser), de drones, et même de serrure physique (oui, une serrure classique toute bête). Et ce, quels que soient les environnements au sein desquels ces systèmes sont utilisés :
- Système d’Information d’entreprise (IT – informatique bureautique & serveur)
- Système d’Information Industriel (OT – Barrage hydraulique, contrôle de commande d’une usine, système de gestion des infrastructures d’une ville…)
- Domotique
- Navire / Avion / Voiture
- Ports maritime
- Etc …
Bref, c’est large. Très large même. Une particularité d’ailleurs, en France, le marché de la cybersécurité s’adresse majoritairement aux entreprises souhaitant protéger leurs Systèmes d’Informations. Les conventions tels que Le Hack mettent d’ailleurs beaucoup plus en avant les méthodologies d’exploitation de vulnérabilités liées à de l’IT. A tel point qu’on en oublie le champ du possible.
La DEF CON rappelle que l’IT ne représente finalement qu’une petite partie de la sécurité numérique, et qu’il est ô combien essentiel de multiplier ses efforts pour sécuriser tout équipement soumis au risque cyber – dont le fonctionnement nominal peut être altérer par une couche logique. Il est probable que nos confrères outre-Atlantique aient une longueur d’avance, et qu’ils ont bien compris que les vulnérabilités ne sont pas présentes que sur des infrastructures informatiques d’entreprises. A voir comment évoluera le paysage de la cybersécurité d’ici quelques années. Wait & See comme on dit.
Comment ?
Comment parle-on de tout ça à la DEF CON ? Moi qui ne suis pas un habitué de ce genre d’événement, je dois admettre que c’est ce qui m’a le plus tracassé lors de la préparation de ma visite. Que vais-je voir ? De manière résumée, on retrouve principalement :
- Des Conférences : A la DEF CON, c’est au bas mot 200 personnes par conférence, dans des salles à très grosse capacité. Et il y’en a 4, occupées en continu par des conférenciers. Beaucoup de monde, beaucoup de sujets, très variés, tout le temps. Ce n’est pas rien.
- Des Workshops : Des exercices techniques, les places sont plus rares (une trentaine par workshop) et on doit s’inscrire à l’avance (plus de disponibilités quelques heures après l’ouverture des inscriptions, on se croirait à un concert d’AC/DC). On vient avec son PC, et on pratique pour découvrir, exploiter, ou comprendre des vulnérabilités. Un minimum de compétences est requis, mais la plupart des workshops sont accessibles aux débutants.
- Des Villages : C’est la partie qui m’a le plus intriguée. Un Village n’est autre qu’un espace dédié accompagné d’un ou plusieurs stands, sur un thème particulier, au sein duquel on peut échanger, assister à des talks (mini conférences), essayer des produits, des systèmes, ou voir comment cela fonctionne (simulateurs de vols, simulateur maritimes…), ou participer à des CTF (Capture The Flag). Les constructeurs et éditeurs en profitent également pour mettre en place des bugs bounty, leur permettant de mettre à l’épreuve leurs produits à moindre coût.
- Des Compétitions : Essentiellement des CTF, mais aussi d’autres compétitions, dont une, portant sur le Badge de la DEF CON, renouvelée chaque année
- Des Démonstrations techniques
- Et encore pleins de trucs cools : des grosses fêtes, des films, des espaces de travail et d’échange, des vendeurs (on parle ici de vendeurs dédiés à l’univers du hack, incluant vendeurs d’habits, de livres, de stickers, des coiffeurs, mais surtout des vendeurs d’équipements électroniques spécifiques… exit les gros vendeurs d’équipements d’infrastructure tels que Cisco CheckPoint Palo Alto Microsoft….), un Wall Of Sheep, affichant les usagers les moins assidus, ayant été hackés durant la DEF CON, et j’en passe.

C'est où et quand ?
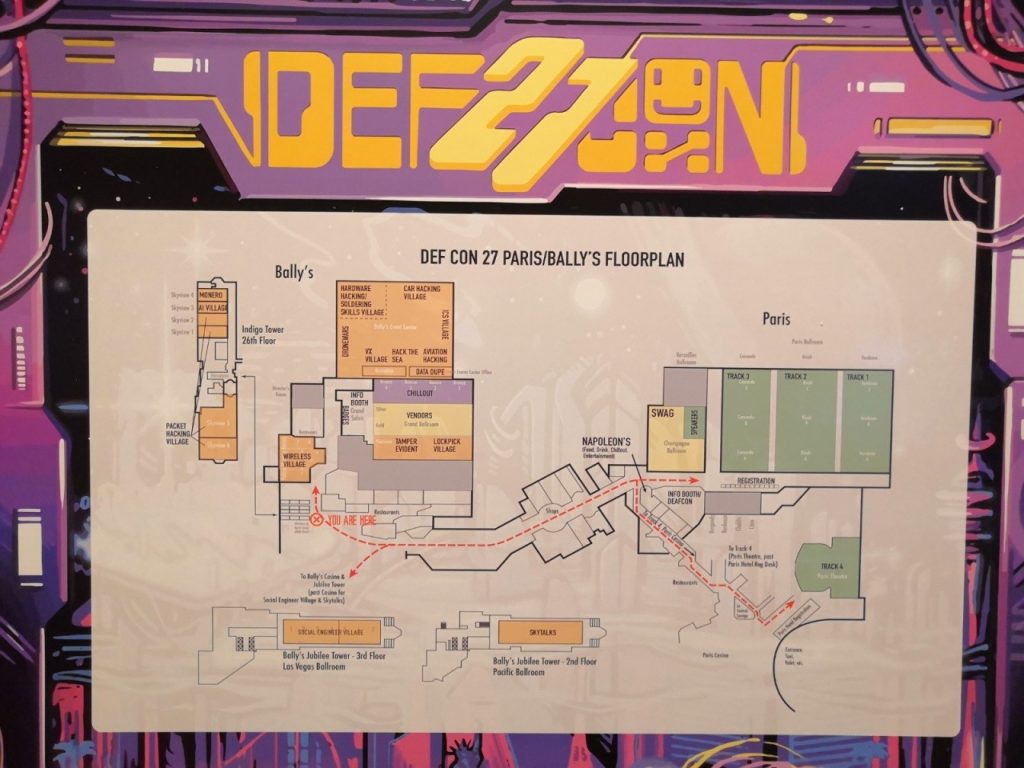
Las Vegas. En l’occurrence, l’édition 2019 s’est déroulée du 8 au 11 aout sur 4 hôtels, et pas n’importe lesquels. On parle du Paris, du Bally’s, du Planet Hollywood, et du Flamingo, 4 des plus prestigieux hôtels du North Strip. Ce n’est donc pas toujours simple de naviguer entre les différentes zones de la convention, surtout lorsqu’on passe d’un hôtel à un autre sous la chaleur écrasante de Las Vegas (plus de 40°). A noter qu’il existe maintenant une DEF CON China à Beijing, se tenant fin mai – début juin.
C'est pour qui ?
Clairement, pour toute personne se définissant comme hacker, ou évoluant dans le milieu du hacking, que ce soit par métier, ou par passion.
Holà, me diriez-vous, n’est-ce pas également pour toute personne évoluant dans la Sécurité Informatique / Cybersécurité ? Et bien, de mon propre avis, oui et non. On peut tout à fait dire qu’un consultant en cybersécurité / intégrateur réseau / gestionnaire de risque / manager de SOC / etc… a totalement sa place dans ce genre d’évènement. Mais (car il y’a un Mais) ! Il ne s’agit clairement pas là du public cible.
La DEF CON, c’est PAR et POUR les HACKERS.
A la DEF CON, on évolue dans un microcosme passionnant et bouillonnant, composé de personnes aux profils variés (allant du bidouilleur au professionnel expert, de la personnalité timide et effacée, au hacker complètement excentrique - ce n’est pas ce qu’il manque). Mais tous sont réunis par une passion commune pour les nouvelles technologies, le bidouillage informatique, et la sécurité OFFENSIVE (voire défensive), et sont dotés de compétences techniques (très) avancées.
Pour les personnes ne correspondant pas à cette description l’évènement reste, quoiqu’il en soit, un incontournable de la cybersécurité. Pas d’inquiétude donc, même si on n’est pas le plus à même de participer aux workshops, on que l’on se retrouvera limité techniquement lors de l’étude d’une vulnérabilité, la DEF CON apporte sans aucun doute des opportunités de rencontre, d’apprentissage, et de découverte de cet univers palpitant.



