Par Rick M. N. H. - TheExpert SQUAD Sécurité
Au travers de cet article, nous commencerons par définir ce qu'est un SIEM (Security Information and Event Management) et quelles sont ses utilités dans le monde d'aujourd'hui, puis nous parlerons des sondes incorporant de l'IA (intelligence artificielle), plus particulièrement de la sonde Cognito de l'éditeur Vectra afin d'exposer ses avantages majeurs pour le monde de demain.
Introduction - Qu'est-ce qu'un SIEM et à quoi sert-il ?
Le but principal d'un SIEM est la gestion des évènements, plus communément appelés logs. Plus précisément, cette gestion est composée de cinq grandes étapes :
- Collecte
- Normalisation
- Agrégation
- Corrélation
- Reporting
La collecte des logs peut se faire à partir de sources hétérogènes telles que des pare-feux, des routeurs, des équipements IDS/IPS mais aussi de formats divers comme Syslog, SNMP ou autres.
Une fois collectés, ces logs sont enregistrés dans un format brut et, dans la plupart des cas, il faudra passer par une étape de normalisation (ou parsing en anglais) afin que ces logs soient reconnus et traités par le SIEM.
Maintenant que ces logs sont dans le format attendu, il est possible de configurer des règles de filtrage afin de ne conserver que les logs ayant une réelle valeur intrinsèque, c'est l'agrégation.
Arrive à présent l'étape critique, celle de la corrélation. Il s'agira d'établir des règles qui, si toutes les conditions sont réunies, lèveront des alertes de sécurité qui pourront être notifiées par mail, SMS ou encore par création de ticket si la solution est interfacée pour le faire.
Enfin, il sera également possible d'établir des rapports et des dashboards si l'on souhaite avoir une vue synthétisée de ces alertes.
D'après le Magic Quadrant du Gartner de 2018 les 2 leaders sur le marché son IBM et Splunk.


Source : Gartner (déc. 2018)
Quelques exemples d'implémentation
Pour faire simple, imaginons que le format attendu pour un log soit :
MMM JJ HH:MM:SS @IP Hostname Product Version EventID Description
Et que l'on reçoive un log qui ne respecte pas ce format, nous serons obligés de passer par l'étape de parsing afin de réécrire le log sous le bon format pour qu'il puisse être compris et catégorisé de la bonne manière par le SIEM.
NB: Les SIEM sont généralement très exigeants sur les formats de logs attendus et ils doivent être parfaitement respectés. Par exemple, si le délimiteur est le pipe ( | ) il faudra bien respecter le format "espace pipe espace" entre chaque paramètre.
Une fois que l'on s'est assuré que les logs étaient bien parsés par le SIEM, on peut essayer de les corréler afin de lever des alertes de sécurité.
Par exemple, créons une règle qui lèvera une alerte si un administrateur a 3 échecs lors d’une authentification en moins de 10 secondes.
- Si USER appartient à ADMINGROUP
- ET Si USER a 3 échecs d’authentifications en 10 secondes
Voilà, c'est fait. Si ces deux conditions sont réunies, une alerte sera levée.
NB: La liste des conditions doit être précise et exhaustive afin de ne pas générer trop de faux positifs (alerte levée sans qu'il y de réelle menace) et il faut impérativement que toutes les conditions soient remplies pour lever l'alerte. Il s'agira donc de trouver le juste milieu entre "faux positifs" et "l'alerte ne sera jamais levé".
Pour résumer, les SIEM sont capables de collecter des logs, détecter des anomalies, lever des alertes de sécurité en cas de menace et générer des rapports si besoin est. Par contre, une configuration manuelle préalable est nécessaire, toutes les conditions doivent être respectées, les règles sont basées généralement sur des @IP et les mouvements latéraux sont difficiles à détecter.
Petite parenthèse : Un mouvement vertical désigne une infiltration d'un attaquant à un niveau de profondeur plus élevé, par exemple dans le cas d'une usurpation d'un compte administrateur. Un mouvement latéral quant à lui désignera une attaque sans pour autant s'être introduit plus profondément dans le système, typiquement si, une fois administrateur, l'attaquant essaie de lire, ou copier des fichiers sensibles.
Vectra Cognito

La sonde Cognito est une sonde incorporant de l'IA. Elle fonctionne en complément d'un SIEM. Son objectif principal est de stopper les attaquants avant qu'ils ne puissent nuire. Elle fournit :
- Un monitoring automatique 24/7,
- De l'auto-apprentissage (machine learning),
- Une meilleure détection que les actuels IDS/IPS/SIEM classiques,
- Une détection basée sur les hostnames et les @MAC et non sur les @IP,
- Un historique des logs en fonction des hostnames et un tracking en temps réel,
- Une détection de quasiment toutes les attaques dès le premier jour, même les mouvements latéraux sans configuration manuelle préalable.
Elle est également capable d'étudier le comportement normal des équipements au sein d'une entreprise et de lever des alertes en cas d'écart. Typiquement, si un administrateur se connecte à tel serveur tous les jours à 12h, elle en prendra connaissance et pourra lever une alerte si un jour un administrateur se connecte à 20h.
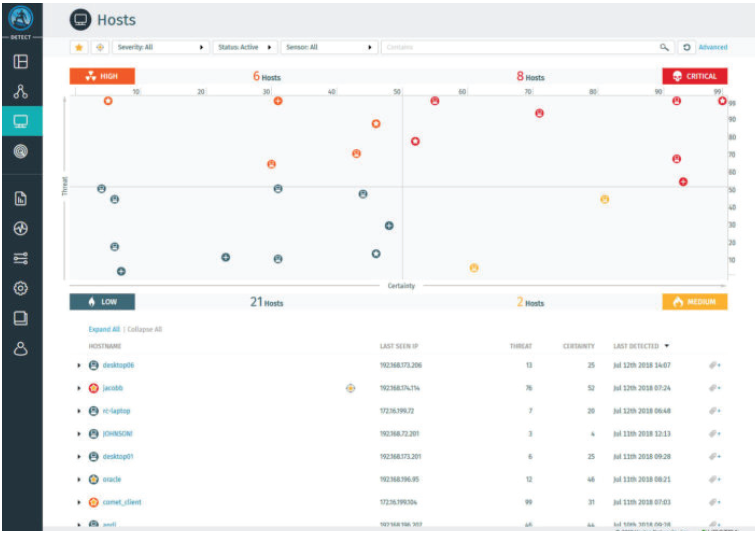
Sur chaque alerte levée, elle positionne deux indicateurs : la menace (Threat) et la certitude (Certainty). La menace indiquera l'impact que cette attaque aura sur l'entreprise tandis que la certitude peut être prise comme un taux de confiance sur le fait que cette alerte soit réelle.
Pour y voir plus clair, prenons deux exemples :
- Le cas d'une attaque par brute force (très grand nombre de tentatives d'authentification en très peu de temps) aura un indicateur de certitude très élevé étant donné que l'on est quasiment sûr qu'il s'agit d'un automate qui teste des milliers de mots de passe, par contre, la menace sera faible car ce type d'attaques est très bien protégé par quasiment toutes les entreprises.
- Le cas d'une attaque où un administrateur souhaite copier des fichiers sensibles aura un indicateur de certitude modéré étant donné que la sonde ne peut pas être sûr que c'est une vraie attaque alors que la menace sera ici très élevée s'il s'avère qu'un attaquant malicieux à usurper l'identité d'un administrateur pour extraire des informations sensibles
De plus, elle détaille le cheminement de chaque attaque qu'elle lève et propose des solutions, ce qui peut faciliter la montée en compétences de personnes juniors dans le domaine mais également aider des personnes plus expérimentés à résoudre les incidents plus rapidement.
Par ailleurs, via l'interface graphique de Cognito, on peut observer un Dashboard avec 4 types de criticité (Faible, Moyenne, Haute et Critique) et une évolution de ses nœuds en temps réel (augmentation ou diminution en criticité voire disparition si l'incident a été résolu).

Vous cherchez une solution efficace pour vous prémunir des cyber-attaques ? Optez pour Vectra Cognito et l'affaire est dans le sac !!