Par Jamel M., Consultant Cybersécurité Squad
La cybersécurité cognitive est une posture qui permet de comprendre les comportements humains artificiels, à travers le fonctionnement des fonctions cognitives, tirés des interfaces humain-machine.
Elle s’appuie sur un type de cognition qui désigne la manière dont les systèmes artificiels acquièrent des données en produisant des représentations, et en les transformant en connaissances par des algorithmes basés sur les fonctionnalités du cerveau en vue de les mettre en œuvre dans les activités et dans les comportements d’un système.
Des fonctions cognitives sont intégrées dans le fonctionnement d’applications et de frameworks en intelligence artificielle, tels que la plateforme IBM Watson IOT, ce qui permet d’introduire d’autres paramètres dans les méthodes d’intrusion de système cible. Aussi, si elles permettent le hacking cognitif d’individus et d’organisations, ils existent des contre-mesures de sécurité cognitive.
Se défendre du hacking cognitif
Le hacking cognitif fait intervenir des systèmes d’auto-apprentissage qui utilisent la disponibilité et l’exploration des données sensibles et non sensibles, la reconnaissance de schémas déterministes que les systèmes utilisent, le traitement du langage naturel dans la construction de différents types algorithmes : K-means, DBSCAN, KNN, WARD, Weka.
Il prend pour cible les fonctions cognitives intégrées dans le fonctionnement d’un système ou d’une application. Le 22 mars 2016, l’attaque contre le cours de bourse de la société Vinci s’est appuyée sur le contenu d’un mail basé sur la fabrication d’un sentiment d’urgence pour court-circuiter le premier niveau de contrôle de sécurité.
Il s’attaque également à la cognition des individus pris pour cible au sein des organisations. Le vecteur principal de ce hacking est lié à l’accès aux données, de sorte que des RSSI, des responsables sécurité, et des responsables en management d’individus sont des diffuseurs potentiels.
Son effet est d’autant plus destructeur lors de phénomène de crise ou dans un contexte humain non apaisé : attentats, crise sanitaire, jalousie, frustration, mauvaise organisation, éducation déterministe, ego non-maîtrisé, frontière privé-public non définie, absence d’éthique professionnelle ou de culture d’organisation saine, surveillance à outrance.
Construire une sécurité cognitive
Elle se définit par une capacité à détecter et à remédier un processus de hacking cognitif produit par la construction d’écosystèmes artificiels d’interprétation de données qui stimulent un comportement amenant à une décision erronée.
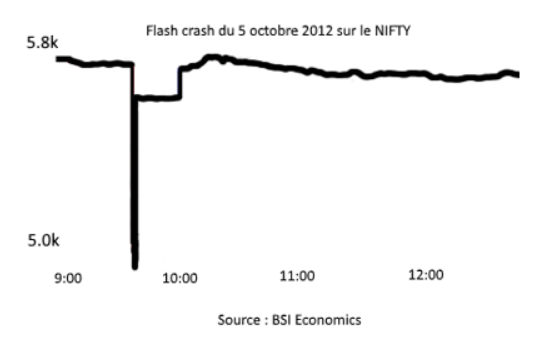
Les algorithmes du trading à haute fréquence ont provoqués, le 5 octobre 2012, une chute brutale de l’indice NIFTY suivie d’une reprise haussière aussi forte.
Elle intervient dans la définition de la connaissance de la menace, dans la détection d’anomalie dans le comportement des systèmes et des organisations, et dans la réponse à incident. Dans chacune de ses phases, la sécurité cognitive est une contre mesure aux vulnérabilités propres des données qui déterminent chaque organisation et individus.
À l’échelle des données, l’application de ces paramètres sont, par exemple, applicables au modèle de données validées qui sont ensuite utilisées par les métiers grâce au modèle prédictif du Machine Learning. Cette technologie se définit par la capacité d’une machine à calculer sur des délais courts un traitement de différents types de données à des fins opérationnels.
À l’échelle des individus, les anomalies comportementales sont les signes de détection les plus visibles. Et les facteurs encourageants relèvent davantage de la psychiatrie liée à l’histoire de chaque individu et la manière dont leurs fonctions cognitives traitent l’information.
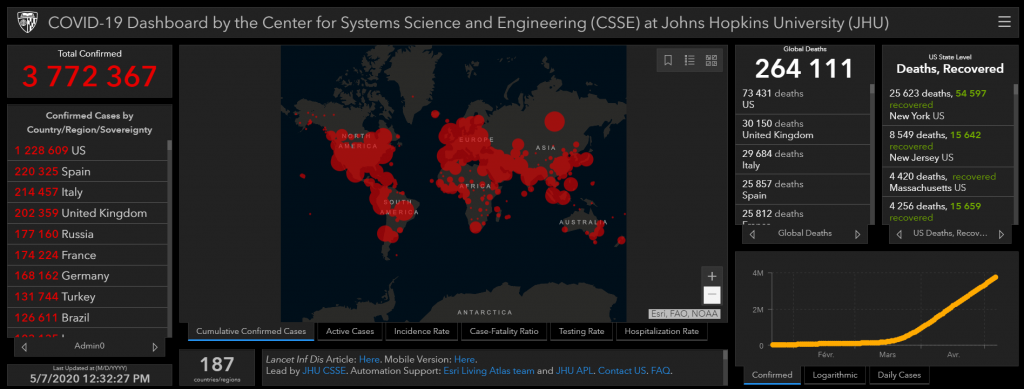
Sécurité cognitive et intelligence d’action : l’exemple d’une crise sanitaire
Face à la crise sanitaire, la difficulté fut de rassembler des points de données sur l’ensemble d’une chaîne impliquant : gouvernance et chaîne médicale. Cette dissonance cognitive engendre des décisions faussées et une difficulté à déterminer les actions à mener. Dès lors, elle offre aussi des attaques d’opportunités en exploitant la faiblesse des mécanismes automatiques prédictifs provenant de données non adaptées et mal configurées.
Au titre de l’attaque DDos du 22 mars 2020 contre les hôpitaux de Paris, elles concourent à diminuer la disponibilité et la performance des plans d’urgence sanitaire. Elles altèrent également la qualité des données lorsqu’il s’agit du malware « Coronavirus Map » qui vise les données cartographiques de l’épidémie et les données à caractère personnelles des utilisateurs.
La remédiation cognitive, dans sa fonction de réparation des altérations causées par une situation nouvelle, prend la forme d’une cybersécurité où des capteurs sont produits pour construire une chaîne de valeur à travers : un algorithme orienté sur le langage naturel avec le « Chatbot COVID 19 » et la mise en place du protocole « Robert » sous la forme d’une application dont l’échelon de coordination est placé au niveau paneuropéen.
Le Bot-COVID 19 s’appuie sur une série de questions/réponses à partir du traitement du langage naturel et la génération automatique de textes. Le Bot interroge une base de connaissances pour lui permettre de répondre à l’objet identifié.
Le protocole « ROBust and privacy presERving proximity Tracing » se caractérise par une architecture sur la technologie Bluetooth et l’utilisation de pseudonymes ("crypto-identifiants"). Un serveur attribue des pseudonymes temporaires. Ces derniers sont échangés permettant de conserver un historique des personnes croisées dans le serveur, de sorte que l’application vérifie si le pseudonyme se trouve dans la liste des personnes infectées, et alerte en cas d’une réponse positive.
Plus d'articles sur la CyberSécurité ⤵


