Par Jordan A., Technical Evangelist Squad
Dans cet article, nous avons souhaité aborder un sujet qui prend de plus en plus d’importance chez nos clients : la microsegmentation.
Dans les pratiques de sécurité, notamment avec l’avènement du Zero Trust, et l’apparition d’infrastructure en micro-services, nous observons que de plus en plus de clients rencontrent de réelles difficultés à maintenir fonctionnelles et évolutives leurs politiques de sécurité. C’est pourquoi nous commencerons par faire un état des lieux des pratiques existantes, puis nous verrons comment passer de la segmentation réseau à base de VLANs, à une microsegmentation efficace.
Il existe plusieurs solutions qui abordent la microsegmentation sous divers aspects : avec des agents, en utilisant les hyperviseurs, ou encore grâce aux équipements réseaux. Nous essaierons d’y voir plus clair avec les différents avantages et inconvénients liés à ces méthodes.
Enfin nous terminerons cet article, en abordant le nouveau partenariat entre Squad et Illumio, pour permettre à nos consultants de monter en compétences et en expertise sur une des solutions de microsegmentation, parmi les plus utilisées aujourd’hui, chez l’ensemble de nos clients.
SOMMAIRE
- Etat des lieux et Zero-Trust
- La segmentation réseau
- Le fonctionnement de la microsegmentation
- Exemple de microsegmentation
- Les différentes approches pour mettre en place la microsegmentation
- Partenariat officiel Illumio
- Conclusion
Etat des lieux et Zero-Trust
Depuis plusieurs décennies, la sécurité informatique s’est surtout concentrée sur la défense périmétrique avec des règles de filtrage basées sur les autorisations ou les interdictions des flux de données au niveau des entrées et sorties des Datacenters. Seulement, les Datacenters ont évolué, avec de plus en plus de solutions de Cloud, d’outils de type SaaS (Software as a Service), ou encore avec le BYOD (Bring Your Own Device) et le télétravail.
De plus, l’utilisation d’architectures en micro-services, remplaçant les « monolithes » applicatifs, a également amené à une multiplication des « workloads » impliquant, une complexité supplémentaire et des besoins plus importants au niveau de la granularité des règles de sécurité.
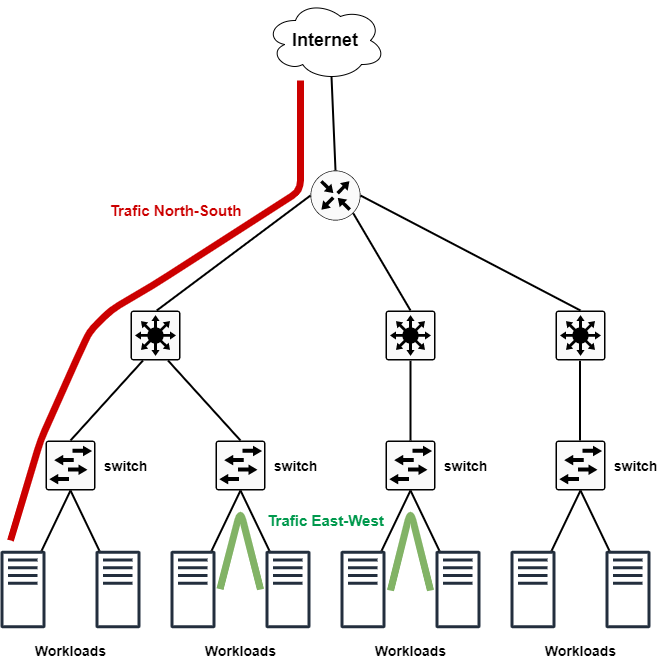
Pour répondre à ces nouvelles utilisations, et ces nouveaux besoins, des solutions de filtrage situées à l’intérieur même du Datacenter notamment concernant le trafic East-West sont apparues. Parmi ces outils, on retrouve notamment la microsegmentation.
On remarque également que le Zero-Trust correspond à modèle de sécurité qui est de plus en plus plébiscité par l’ensemble des acteurs du secteur. En effet, nous considérons alors qu’aucun utilisateur ou service n’est digne de confiance à 100%. Ainsi, si une de nos ressources a été compromises, elle ne pourra pas compromettre toutes les autres ressources de notre SI.
La segmentation réseau
Jusqu’à présent, les VLANs ont été utilisés pour segmenter le réseau d’une entreprise, notamment pour isoler logiquement les différents services (éviter que des salariés du Marketing puissent accéder aux serveurs de la comptabilité par exemple). Ainsi les équipements appartenant à un même VLAN peuvent communiquer entre eux sans restriction particulières, alors que ceux situés sur des VLANs différents, ne peuvent pas communiquer (sauf via du routage inter-VLAN).
Cependant, même en utilisant la technologie des Private-VLANs et des VXLANs, nous nous trouvons confronter à la problématique de la sécurisation des communications à l’intérieur d’un même VLAN. En effet, il reste possible d’effectuer des règles de pare-feu individuelles sur chaque serveur, mais dépassé un certain nombre d’équipements, cette gestion devient vite impossible.
Enfin, nous trouvons une autre limitation concernant la création des règles de sécurité. En effet, pour identifier les équipements, nous utilisons principalement l’adresse IP, et pour identifier les services, nous utilisons les ports TCP et/ou UDP. Or que se passe-t-il si ces éléments viennent à changer ? Il faut revoir l’ensemble des règles et politiques de sécurité pour les faire correspondre aux nouvelles informations d’identification de ces équipements. Autant vous dire, qu’il s’agit d’une tâche colossale sur un Système d’Information (SI) de taille importante…
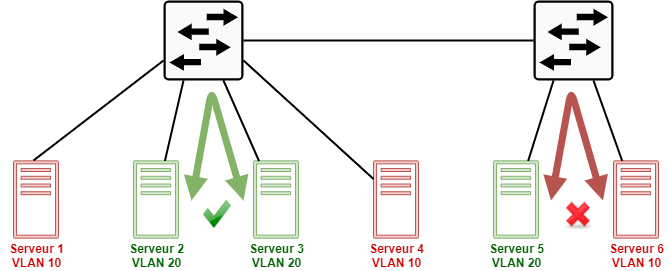
Dans le schéma ci-dessus, les serveurs 1, 4 et 6 appartiennent au même VLAN, ils peuvent donc communiquer ensemble sans restriction par défaut. De même pour les serveurs 2, 3 et 5. Cependant, la communication ne peut s’effectuer entre deux serveurs appartenant à des VLANs différents (comme le serveur 5 et 6 par exemple) sans mise en place de routage inter-VLAN.
Le fonctionnement de la microsegmentation
La microsegmentation, ne se base plus uniquement sur les adresses IPs et les ports pour la création des politiques de sécurité. En effet, ce contrôle peut se baser sur de multiples critères : des labels, l’état de l’anti-virus, les versions de certains logiciels, l’environnement dans lequel se situe le workload, etc… Les serveurs peuvent ainsi être placé en « quarantaine » s’ils ne respectent pas certains critères, ou s’ils ne répondent plus correctement, ce qui empêche leur communication avec tous les autres workloads du SI.
Le concept principal qui précède la mise en place de la microsegmentation, correspond à une cartographie des flux temps réels. Ainsi, il est possible de visualiser l’ensemble des communications des différents workloads entre eux, et notamment pour connaître plus précisément les échanges entre les serveurs (ou conteneurs) d’une même application, ou d’applications différentes. Nous pouvons ainsi avoir une connaissance approfondie des dépendances applicatives.
La création des politiques de sécurité au niveau de la microsegmentation se fait principalement via l’utilisation des labels suivant l’acronyme RAEL, pour identifier les applications par :
- Rôle (Master Node, Base de données, Serveur Web, etc…)
- Application (Messagerie, Drive, Annuaire, CRM, etc…)
- Environnement (Prod, Pré-prod, Recette, etc…)
- Localisation (New York, Paris, Lyon, Madrid, etc…)
Les restrictions de communication se basent ainsi sur des « labels » (noms) plutôt que sur des IPs ou des Ports afin de permettre une meilleure compréhension, et une évolutivité plus forte de l’infrastructure.
Exemple de microsegmentation
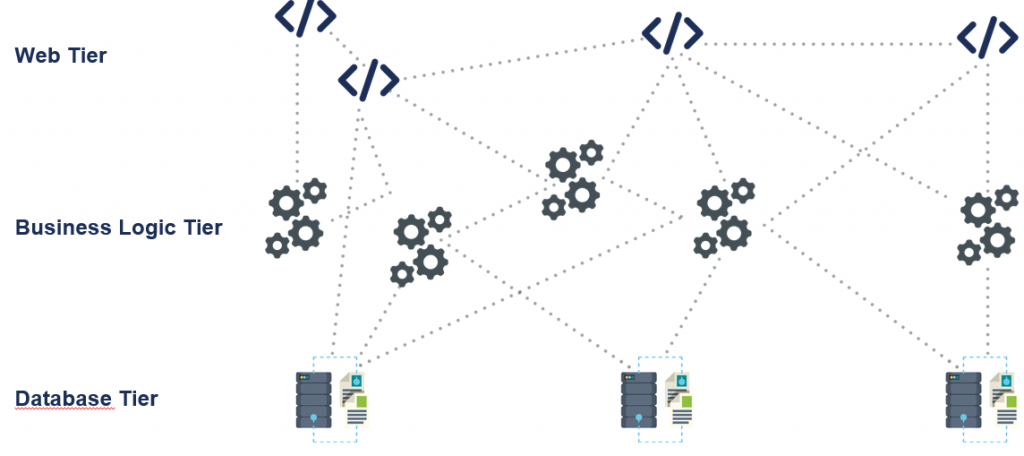
Sur le schéma ci-dessus, on voit environ 3 applications différentes, composés de plusieurs Tiers : Web Tier, Business Logic Tier, et Database Tier. Il est assez intéressant de noter qu’il s’agit d’une architecture en microservices avec les différents services séparés les uns des autres.
Cependant, si ces applications sont situées sur le même VLAN, ou sur des zones où les communications internes sont possibles, on peut se retrouver en difficultés. En effet, que se passerait-il si une de ces « briques » soit compromise ? Comment peut-on être sûr que l’attaquant ne peut pas compromettre les autres services ou les autres applications ?
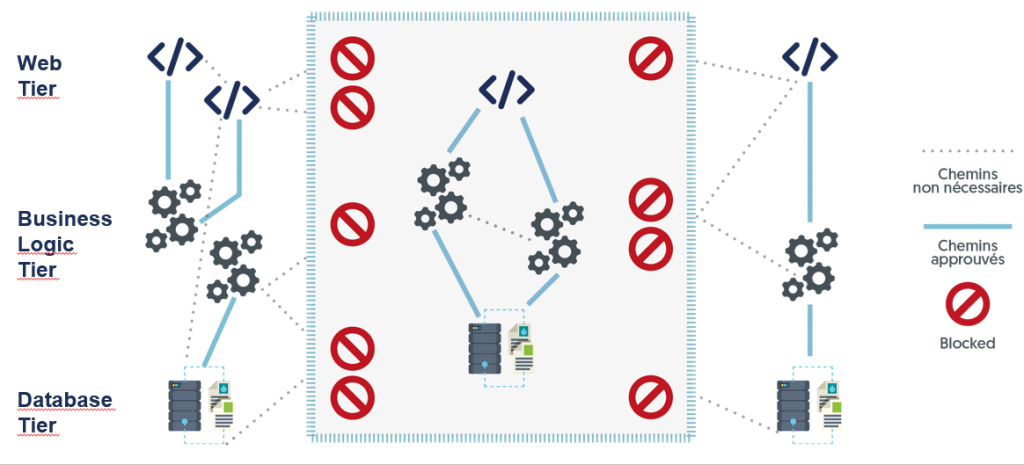
Le schéma ci-dessus représente la même architecture microsegmentée, notamment au niveau de l’application du milieu. En effet, les communications entre les différents Tiers sont autorisées, car nécessaire du fait de l’interdépendance applicative, mais les autres communications sont bloquées.
Or si vous observez bien ce schéma, il n’y a pas mention de Firewall. En effet, les politiques de sécurité peuvent être directement implémentées au niveau de chaque workload (comme dans la solution Illumio®), plutôt que sur un équipement tier type firewall.
Les différentes approches pour mettre en place la microsegmentation
Comme vous avez pu vous en rendre compte, la microsegmentation touche plusieurs aspects du système d’information, notamment : réseau, sécurité et système. Il y a donc plusieurs approches pour mettre en place ce type de solution sur votre infrastructure.
Utilisation d’agents
Nous pouvons trouver des solutions de microsegmentation se basant sur l’utilisation d’agents (comme chez Guardicore ou Illumio) à installer sur les Workloads qui font parties de l’infrastructure.
Ce type de solution offre une réelle souplesse, donnant la possibilité à la solution de vérifier les divers éléments du workload (versions, OS, ports ouverts, communications actives, etc…) de manière extrêmement fine. De plus, dans la plupart des cas, si les agents perdent la connectivité avec la solution centrale, ils continuent d’appliquer les règles les plus récentes.
Cependant, l’utilisation d’agents impliquent également quelques inconvénients comme la prise en charge et la compatibilité des systèmes d’exploitation, ou l’impact potentiel sur les performances de l’équipement (au niveau RAM et CPU).
Utilisation de composants hyperviseurs
Nous pouvons trouver des solutions de microsegmentation se basant sur l’utilisation des composants existants sur l’hyperviseur utilisé. Cette solution trouve son intérêt, surtout lorsque l’infrastructure est basée sur du VMWare notamment via son composant NSX.
On obtient ainsi un fonctionnement indépendant de la ressource qui est protégée, mais sa mise en place est assez complexe, et ne prend pas directement en charge les composants de l’infrastructure qui ne seraient pas virtualisés.
Utilisation de composants réseaux
Comme on pouvait s’y attendre, c’est Cisco que l’on retrouve principalement sur ce créneau. En effet, avec sa solution ACI (Application Centric Infrastructure) on se retrouve à mi-chemin entre SDN (Software Defined Network) et Microsegmentation.
Cette solution est intéressante, car compatible avec beaucoup d’hyperviseurs, et basée sur une nouvelle architecture de type spine-leaf.
Cependant, du matériel spécifique est nécessaire pour utiliser Cisco ACI (Switches Cisco Nexus 9000 series), impliquant un coût supplémentaire pour le remplacement des switches existants.
Squad est partenaire officiel Illumio

De nombreux clients ont déjà rejoint l’aventure de la transition vers la microsegmentation, afin d’améliorer la gestion de la sécurité de leur SI. Squad a décidé d’établir un partenariat avec la solution Illumio reconnue comme l’une des plus performantes aujourd’hui, avec de nombreux clients Français : Natixis, SalesForce, Société Générale, BNP Paribas, etc…
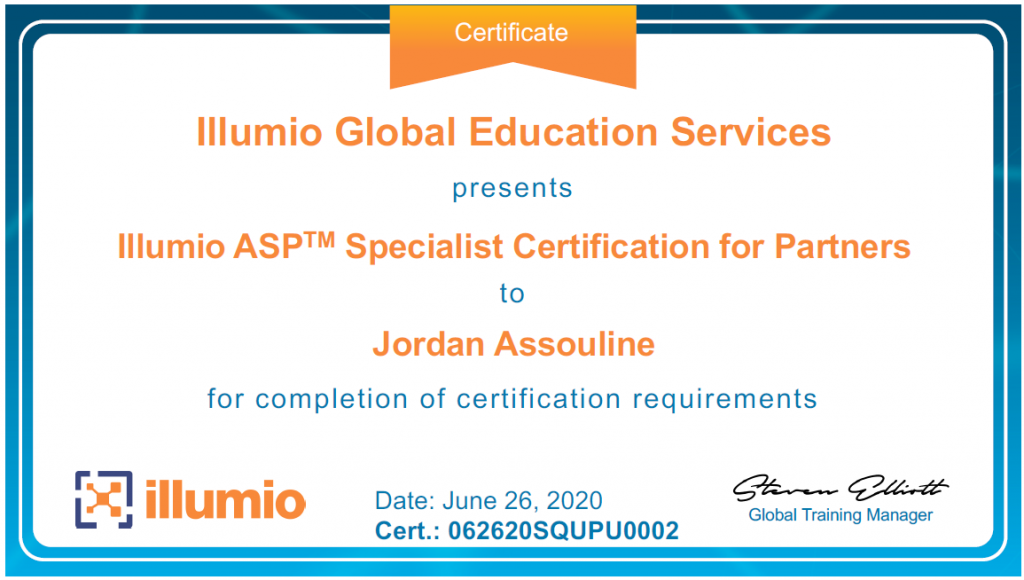
Des sessions régulières sont réalisées entre Squad et Illumio, pour former et certifier nos consultants sur l’utilisation et la mise en œuvre de l’ASP (Adaptive Security Platform), notamment via le passage de la certification : Illumio ASP Specialist Certification for Partners.
Dans cette optique Squad vous accompagnent à la transition et à la gestion de vos solutions de microsegmentation Illumio.
En effet Illumio présente plusieurs avantages :
- Protection de 80% du trafic des Datacenters et du Cloud (Est-West)
- Détection immédiate des activités non autorisées et neutralisation des brèches
- Diminution du nombre de règles de firewall de plus de 95% à l’intérieur du Datacenter
- Fonctionnement dans des environnements virtualisés, conteneurisés, on-premise, Cloud ou Hybrides
Conclusion
La microsegmentation n’est pas un concept récent, puisqu’il existe depuis déjà plusieurs années. Il est tout simplement cohérent avec la mouvance du Software Defined, qui consiste à penser et utiliser l’infrastructure comme s’il s’agissait d’un logiciel.
Peu importe la solution que vous choisirez, sa mise en place et son administration doit être réfléchie et adaptée à vos besoins. Il est cependant, plus que probable, que toutes les infrastructures de taille importante se dirigent vers ce type de solution dans un futur plus ou moins proche.


