Since Friday, December 10, a so-called "zero-day" vulnerability has been causing a stir in the Java world. It is actually a vulnerability in Apache Log4J, one of the most widely used libraries by Java applications. However, mitigation solutions are available.
Zero-day vulnerabilities are the most feared in cybersecurity because they concern vulnerabilities that have not been identified identified or that have not yet received patches. This Log4j vulnerability was quickly labeled a zero-day vulnerability. However, this vulnerability has actually been known for years, as evidenced by the 2016 BlackHat conference.
The criticality and exploitability levels of the Log4J flaw make it a very high-risk vulnerability. Worst-case scenarios are possible: attacking a server with a simple HTTP request without authentication allows any attacker to remotely execute the desired code (RCE): delete or create files, retrieve passwords, etc.This is a real open door to all kinds of intrusions!
However, it is important to note that in order to be vulnerable, versions 1.x must meet a specific condition, as indicated by CERT-FR:
"Version 1 of log4j was initially declared vulnerable, however the vulnerability only exists if the JMS Appender component is configured to take JNDI into account. It is therefore a very specific configuration."
CERT-US
Nevertheless, faced with this flaw, the companies concerned are already on high alert to urgently provide the necessary fixes and responses.
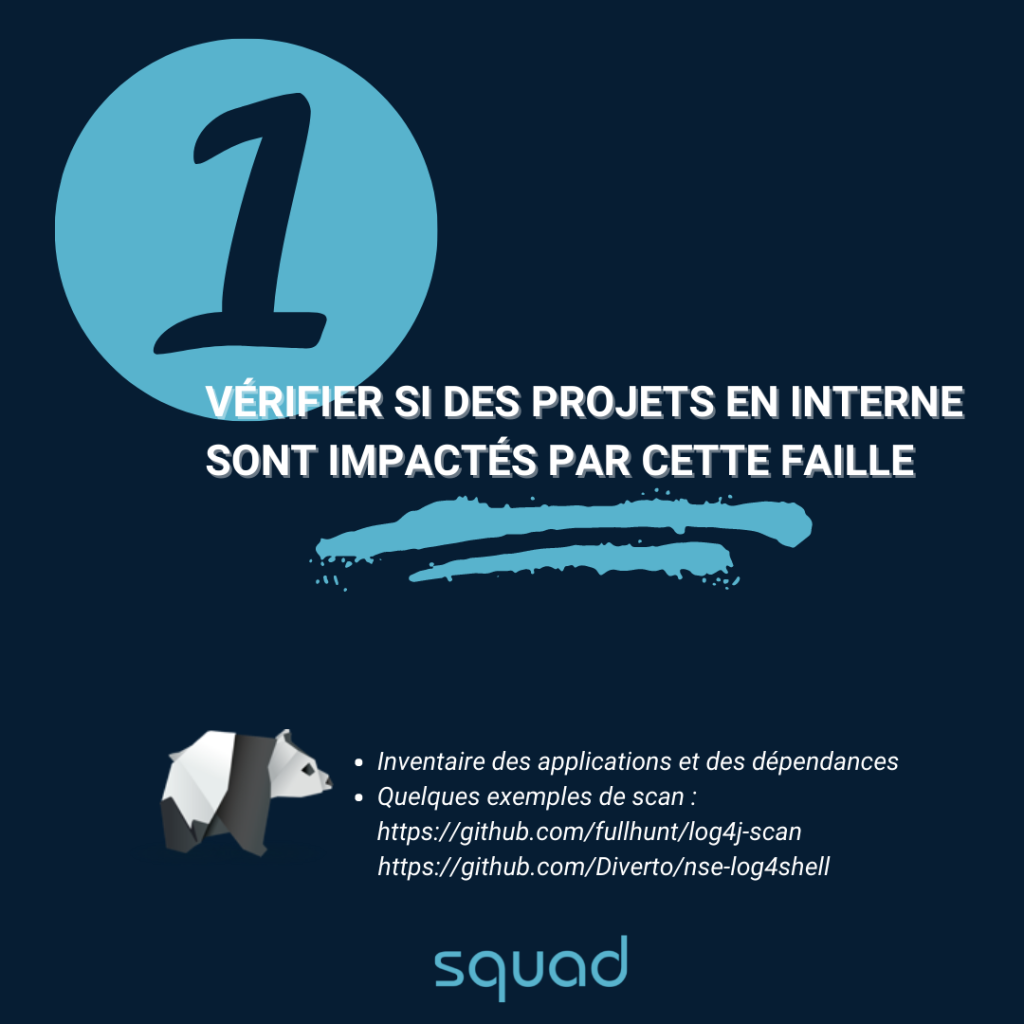
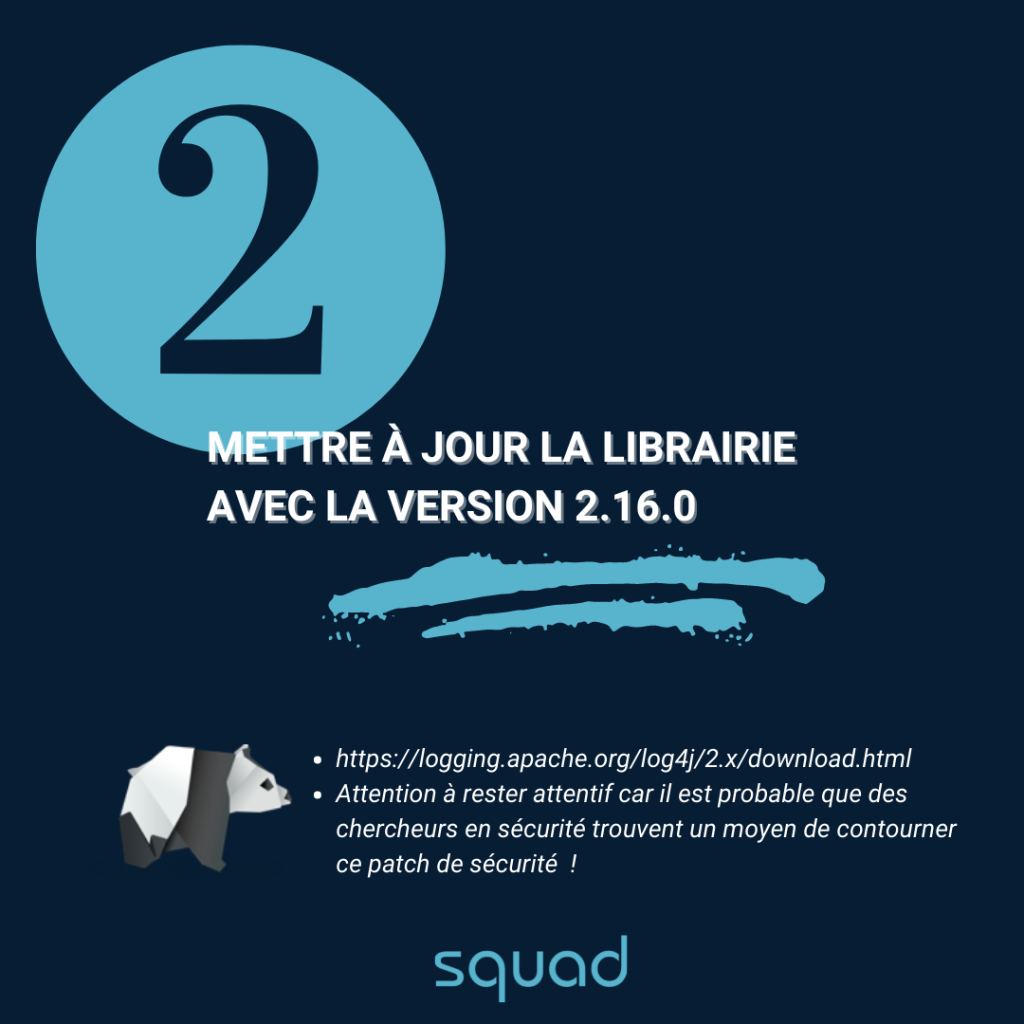
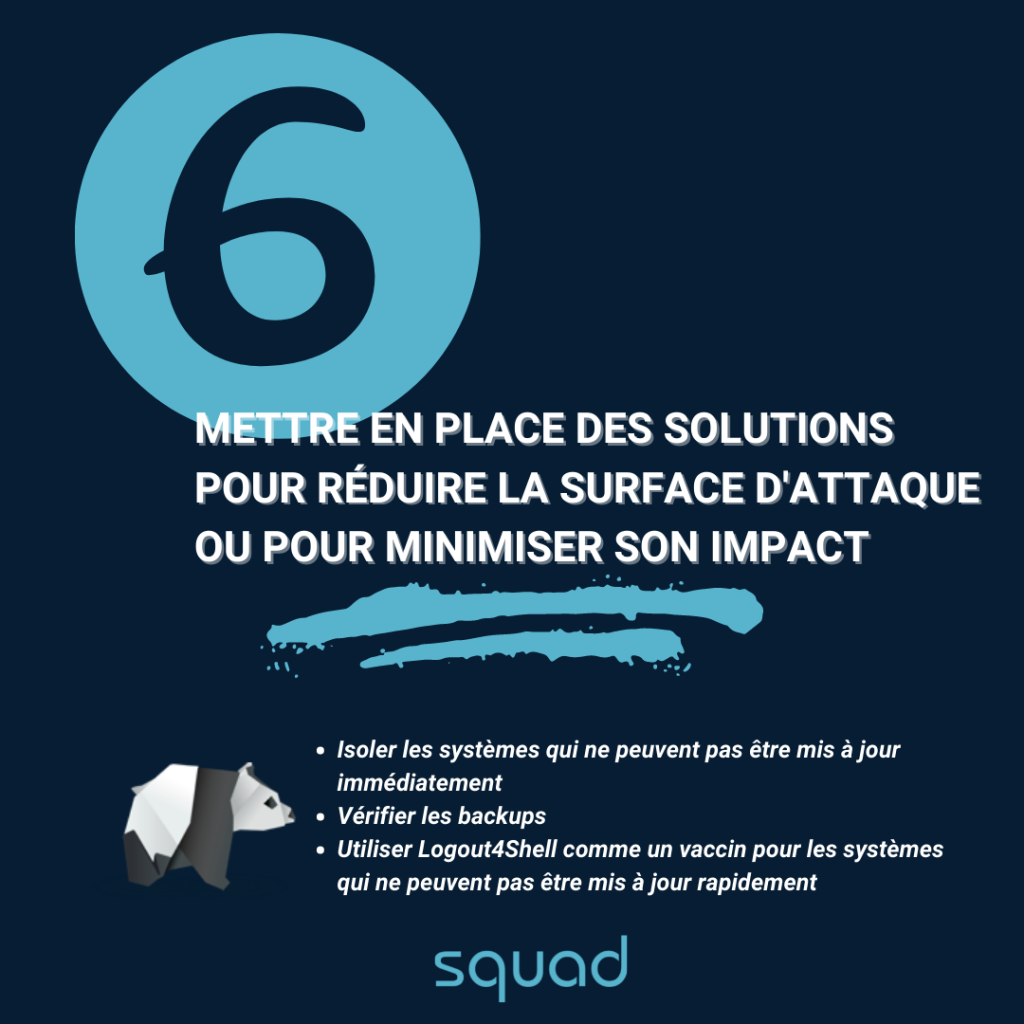
Our hot tips?

To go further
European national CERTs have mobilized to maintain a list of software affected by this vulnerability. Find it here.
More real-time information on theCERT-FR alert bulletin.


