After participating in Hack 2023, attending numerous conferences, and taking part in several workshops, it's time to reflect on these two days. A feedback session led by Didier Zanello and Mickaël Dangleterre, experts at our Nantes agency.
Each edition of this event features a packed and exciting program:
- Participate in various conferences/rumps,
- Participate in various workshops
- See friends and acquaintances again
- Discuss the topics covered in the conference
- Participate in Bug Bounty, various challenges, CTF, etc. (and I'm sure I'm forgetting some)
In short, this leaves us little time to wander around. Once again, most of the conferences were interesting, but let's take a look back at the ones that particularly stood out for us:
Inside Black Hat: Defending one of the most hostile networks in the world
This fascinating conference, hosted by Grifter, showed us the path to take in order to set up and supervise the network used during the Black Hat conference.
After presenting the architecture of the network that has been set up, Grifter moved on to the topic that interests us all: what really happens at these conferences?
The Black Hat conference is one of the most important conferences in the world of cybersecurity. All kinds of people attend (both good guys and bad guys), each with their own objectives, of course. Some come for training, others for the conferences, others for the workshops, others to cause harm, etc. There are also a lot of rumors going around saying that you shouldn't bring your phone to these conferences, that you should use a VPN at all times, etc.
However, the rules remain simple: anything that is illegal remains illegal, but everything else is permitted. And that's it!
No, I'm joking, but it does allow you to see all kinds of things. He told us that the supervisors saw all kinds of sniffing, various attacks presented during the different workshops, all kinds of connected objects during their interventions, but also real attacks, whether on internal workstations/networks or even attacks targeting external networks with the clear intention of causing harm.
In the latter type of flow, the NOC/SOC team intervened, and a simple intervention on their part was enough to silence the most dangerous elements. In fact, monitoring is able to identify specific workstations and users, allowing them to target individuals effectively. In addition, everything that passes through the network is logged. This deters the most aggressive members from continuing their attacks when the supervision team intervenes.
As for the anecdotes he shared with us and the gadgets found on site, there was a bit of everything: USB drives scattered on the floor with suspicious content, all kinds of connected devices of varying degrees of sophistication, etc. We don't realize how different the mindset is between what happens at these conferences and what we might experience in France or at other conferences.
As he also explained, the supervision team uses log reports to raise awareness in real time, particularly when they see passwords, credentials, or other sensitive information in plain text. During these interventions, it is customary to provide a brief reminder of best practices (which he did not hesitate to reiterate during his conference). Once again, we cannot stress enough the importance of always being careful with our data.
Finally, contrary to what one might think once again,the number of members of the deployment and supervision team is not that large for an event of this kind.
To conclude, this conference is simply excellent, and I can only recommend that you watch it again when it becomes available on the HZV YouTube channel.
From Windows driver to EDR
During this talk, Aurelien CHALOT focuses on how antivirus software works. In his presentation, he raises awareness about the means necessary to interpret the actions of these programs. The solution came from a feature of the Windows OS called Kernels Callbacks. However, antivirus software developers (McAfee, Symantec, Kaspersky, etc.) have not always facilitated relations by working hand in hand with Microsoft, following the deployment of PatchGuard (on Windows XP). In fact, it prevented access to and modification of the kernel...and therefore the functioning of antivirus software. Since then,Microsoft has offered an alternative: the WDF (Windows Driver Framework) framework. Windows Driver Framework) comprising the Kernel Mode Driver Framework and the User Mode Driver Framework. The first provides access to all kernel features but seems difficult and very risky to use (due to potential kernel panic), unlike the second. 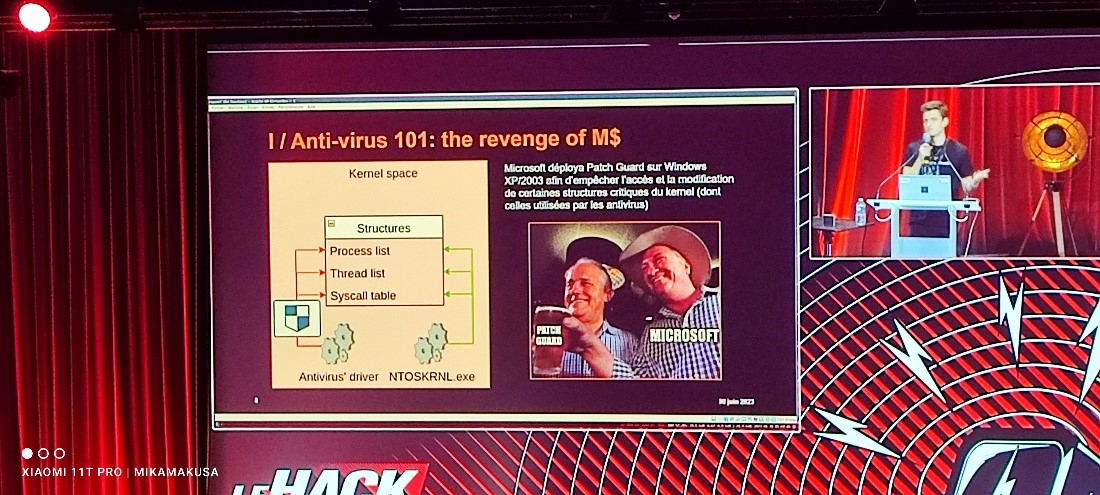
Lambda Malware: the hidden threat in Excel spreadsheets
The duo of Yonathan Baum and Daniel Wolfman, two cybersecurity researchers, gave us a history of the types of malware that can be contained in an Excel file. From macros to the use of Lambdas, via VBA and .NET with information obfuscation to hide malicious payloads. They also treated us to a short technical demonstration of How can an Excel file containing malware escape antivirus detection?
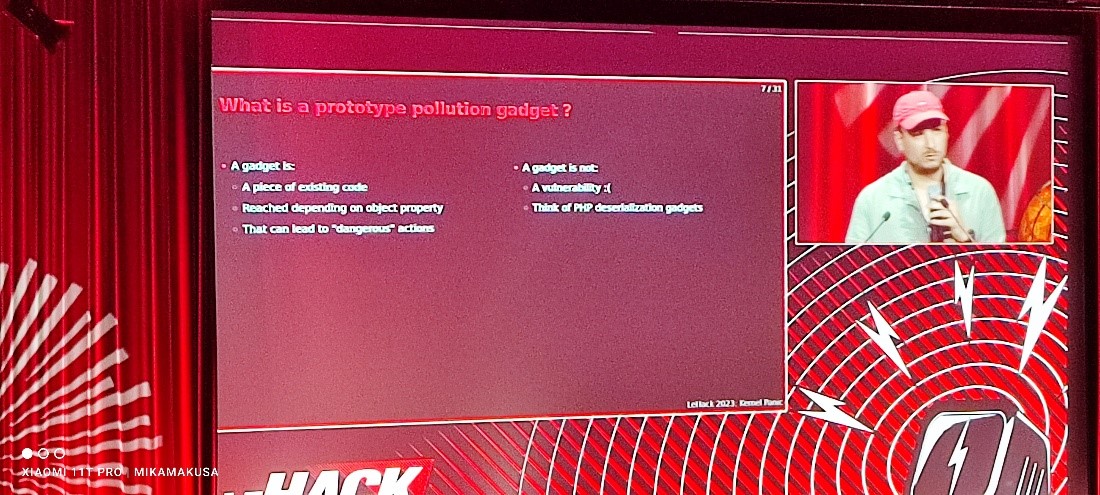
Prototype pollution and where to find them
Here, we are talking about BitK, a technical ambassador, and SakillR, an R&D developer, who came to explain what JavaScript prototypes are and how to find them in a very simple way, even for beginners. They also demonstrated how to pollute these same prototypes for malicious purposes, in order to introduce exotic properties to certain objects, leading to unexpected behavior and potentially allowing the attacker to execute arbitrary code.
The real goal of this intervention is to use a tool developed by and for themselves to help identify potentially dangerous objects by instrumenting the source code via a technical demonstration targeting some of the most widely used JavaScript libraries.
Server hijacking for fun and profit
The contribution of Damien Cauquilfrom Virtualabs was perhaps the most... entertaining... even if that's not really the right word to describe how to hijack a web server by storing files on it... without the knowledge of the administrator in charge of it.
Obviously, this action should not be replicated at home (yes, just like wrestling)! Potentially illegal, it is not really dangerous because it does not affect the data on the server in question, although a demonstration is carried out and best practices are shared in order to avoid this type of situation.
ZFS Raiders of the Lost File
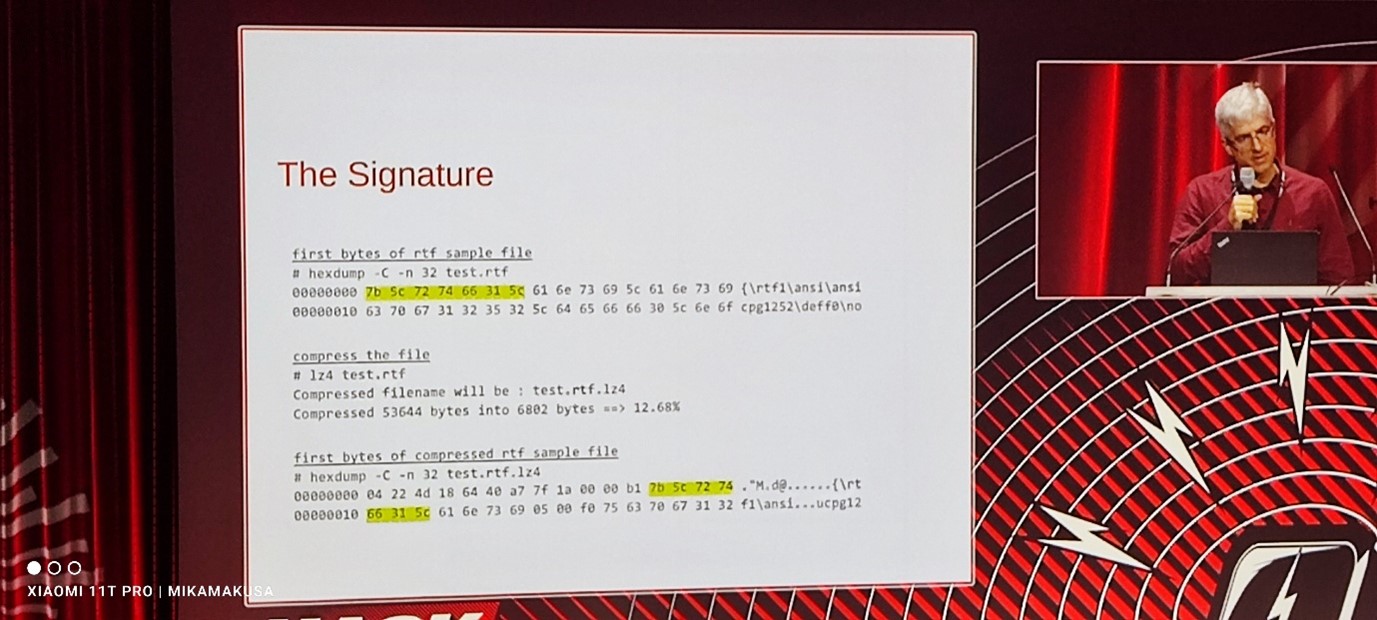
Nikolaos TSAPAKIS explains in this talk how, after wanting to throw away an old hard drive, he tried to recover a file from the ZFS partition on that drive.
After creating an image of the disk, he began searching for the file using its hexadecimal signature (remembering the file extension and size) and, once he found the correct header, decompressed the data block and rewrote the file.
All with the help of a Python script. A truly fascinating conference!
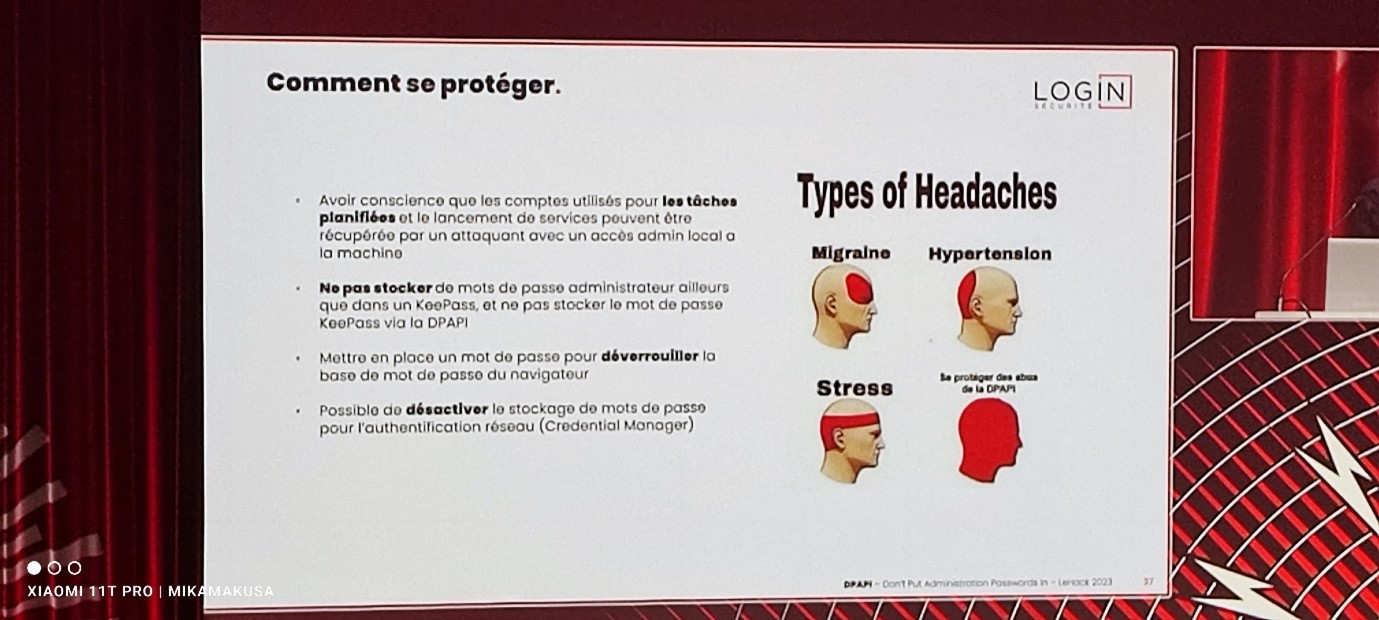
DPAPI - Don't Put Administration Passwords In
Thomas SEIGNEURET and Pierre-Alexandre VANDEWOESTYNE, both from Login Sécurité, came to present DPAPI, a Windows API made available to developers for the purpose of storing user secrets so that they do not have to manage the cryptographic part. But that's not all. Taking an offensive security perspective, they also explained and demonstrated how an attacker could exploit potential vulnerabilities in this API, explaining the various protective measures that could be put in place to limit their exploitation.
In conclusion, we have only one recommendation to make: attend this unique event! With conferences, workshops, challenges, and a great atmosphere, you'll find something to suit you and have the chance to meet some incredible people!